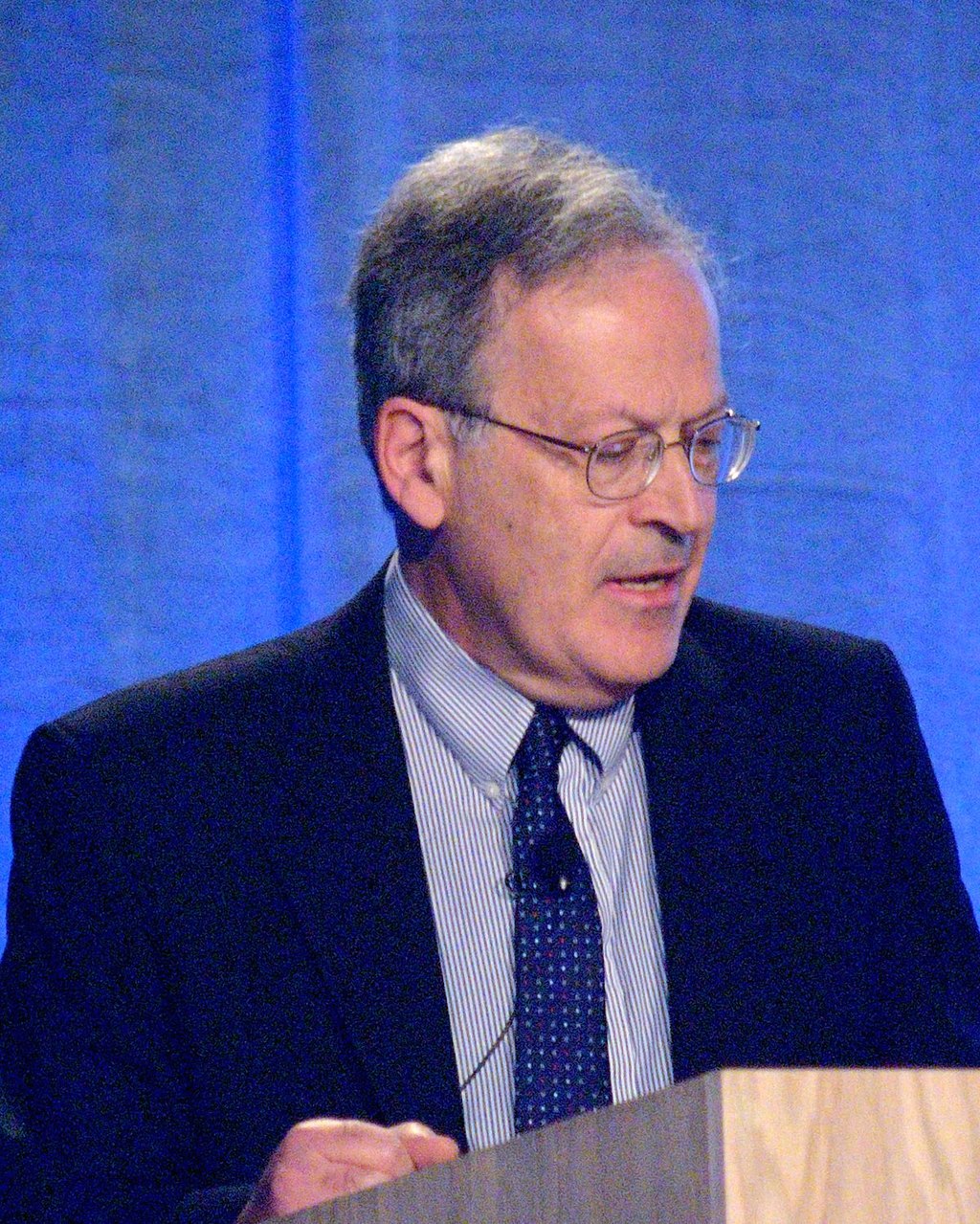
T. Jefferson Coolidge Professor of Computer Science and Applied Mathematics,
School of Engineering and Applied Sciences, Harvard University.
Title: Reasoning on Uncertain Learned Data
Brief Abstract: This basic question faces humans in everyday experience. It is also an important technological problem if we are to make good use of the power of machine learning. In this talk this question will be discussed in the framework of a new theory of human capabilities for information processing.
Bio: Leslie Valiant was educated at King's College, Cambridge, Imperial College London, and
the University of Warwick, where he received a PhD in computer science in 1974.
He won the Turing Award in 2010 with a citation that reads,
"For transformative contributions to the theory of computation, including the theory of probably
approximately correct (PAC) learning, the complexity of enumeration and of algebraic computation,
and the theory of parallel and distributed computing."
Other accolades include the Nevanlinna Prize in 1986,
the Knuth Prize in 1997, and the EATCS Award in 2008. He was elected a Fellow of the Royal Society (FRS)
in 1991, a Fellow of the Association for the Advancement of Artificial Intelligence (AAAI) in 1992,
and a member of the United States National Academy of Sciences in 2001.
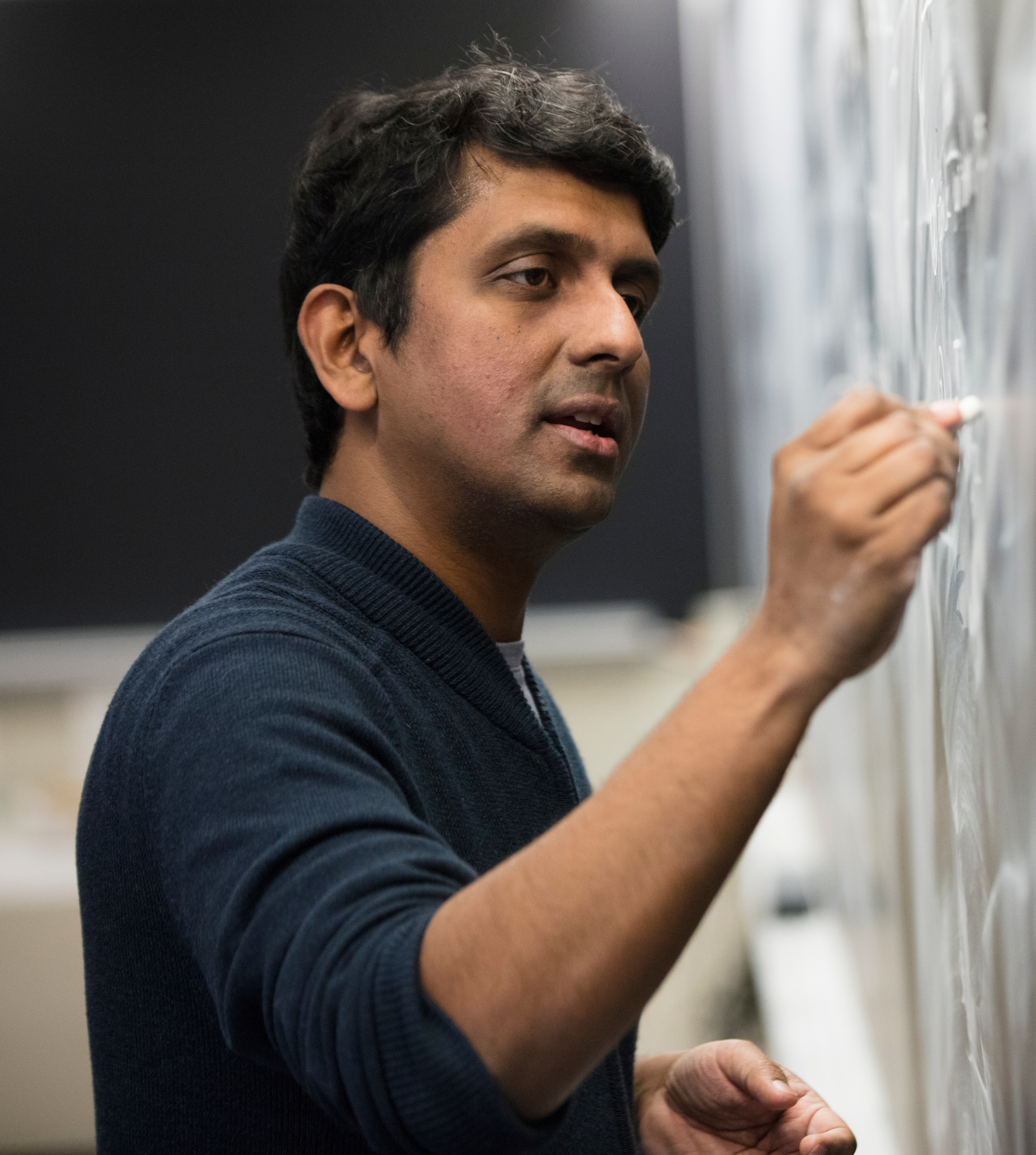
Professor and Chair, Computer Science
Stony Brook University - SUNY
Title: Passive Backscattering RF Tag Networks - Fundamentals and Applications
Abstract: We consider a new generation of Internet-of-Things (IoT) technology that uses 'passive'
backscattering RF tags operating in an extremely low-power regime.
The most common use of such tags is in RFID technology, where a separate active radio transceiver ('reader')
is used to communicate with the passive tags. However, this limits the scalability and broad
applicability of such tags. Our work considers recent advances where such passive tags can
communicate among themselves without any active radio device. In this talk, we will describe the
fundamental technology of such tag-to-tag communication, including techniques to improve the range and
robustness of the tag-to-tag links. We will also describe a novel RF-based sensing technique to estimate
the tag-to-tag channel parameters and showcase how such sensing can enable wide-ranging applications
including localization and monitoring.
Bio: Samir R. Das is Professor and Chair of the Department of Computer Science at Stony
Brook University - SUNY. His research interests are in wireless networking and mobile
computing, focusing on protocols, systems, applications and performance evaluation.
His work on multihop wireless networks is widely cited. He is a past NSF CAREER
award recipient. He co-chaired the technical program committees of premier mobile
networking conferences such as ACM MobiCom and ACM MobiHoc. He served on the
editorial boards of major networking journals, including IEEE/ACM Transactions on
Networking and IEEE Transactions on Mobile Compting. More information about him
and his research can be found at
here.
Professor, Computer Science, MIT
Title: Theoretical Foundations of Real-World Cryptography
Abstract: Block ciphers (aka Pseudorandom Permutations) are the workhorses of modern cryptography.
An overwhelming fraction of Internet traffic is secured using the Advanced Encryption Standard (AES),
a block cipher; the same goes for encrypted file systems, encrypted messaging, and several other
applications we use all the time. In this talk, I will describe a new research program, together with a
collection of recent results, aimed at achieving a foundational mathematical understanding of block ciphers.
Bio: Vinod Vaikuntanathan is a professor of computer science at MIT and the chief cryptographer at
Duality Technologies. Vinod is the co-inventor of modern fully homomorphic encryption
systems and many other lattice-based (post-quantum secure) cryptographic primitives.
His work has been recognized with several awards including the Simons Investigator Award (2023),
Gödel Prize (2022), Harold E. Edgerton Faculty Award (2018), DARPA Young Faculty Award (2018),
the Sloan Faculty Fellowship (2013) and the Microsoft Faculty Fellowship (2014).
He holds SM and PhD degrees from MIT and a BTech degree from the Indian Institute of Technology Madras.
Co-founder & Co-CEO
Swirlds Labs
Title: Hashgraph Consensus
Abstract: The hashgraph consensus algorithm allows multiple computers to
reach agreement with finality in a way that is very fast and very secure
(Asynchronous Byzantine Fault Tolerant: ABFT). We will talk about some of the ideas behind it,
how it works, how this affects blockchain and Distributed Ledger Technology (DLT), and some of the
areas where research is ongoing.
Bio: Dr. Leemon Baird is the inventor of the hashgraph distributed consensus algorithm,
Co-founder of Hedera, and Co-founder and Co-CEO of Swirlds Labs. With over 20 years of
technology and startup experience, he has held positions as a Professor of Computer Science at
the US Air Force Academy and as a senior scientist in several labs. He has been the Co-founder of
several startups, including two identity-related startups, both of which were acquired.
Leemon received his PhD in Computer Science from Carnegie Mellon University and has multiple
patents and publications in peer-reviewed journals and conferences in computer security,
machine learning, and mathematics.
Professor, Computer Science
Ben-Gurion University
Title: One-Way Functions Candidates Based on Information Theoretical Secure Primitives
Abstract: The talk consists of recently proposed one-way functions (OWF) candidates that employ perfect and provable information theoretical secure techniques, for example, one-time pad and secret sharing.
The potential of leveraging the unique properties of, secret sharing, one-time pad, and random permutations in the design of effective one-way functions is the exploration motivation.
For example, one such design involves applying the exclusive-or (xor) operation to two randomly chosen strings. To address concerns related to preimage mappings, we incorporate error detection codes. Additionally, we utilize permutations to overcome linearity issues in the computation process. In order to enhance the security of our approach, we propose the integration of a secret-sharing scheme
based on a linear polynomial. This helps mitigate collisions and adds an additional layer of perfect security. We thoroughly investigate the interactions between different aspects of one-way functions to strengthen the reliability of commitments. Lastly, we explore the possibility of nesting one-way functions as a countermeasure against potential backdoors. Through our study, we aim to contribute to the advancement of secure encryption techniques by leveraging the inherent strengths of the one-time pad and carefully considering the interplay of various components in the design of one-way functions.
The talk is based on recent works in collaboration with Asaf Choen, Pawel Cyprys, Hagar Dolev, Oded Margalit, and Shlomo Moran.
Bio: Chair Professor, IEEE Fellow, EAI Fellow, and founding chair of the department of computer science
of the Ben-Gurion University of the Negev, served as faculty of Natural Science Dean, Chair of the
Board of the Inter-University Computation Center (IUCC first ISP of Israel). Currently, he is the
Computer Science Discipline Committee Chair in the Israeli Education Ministry. He published more
than 400 publications and patents in computer science, distributed computing, networks,
cryptography, security, optical and quantum computing, nanotechnology, brain science, and
machine learning. Dolev authored the Self-Stabilization book published by MIT Press and
collaborated with Deutsche Telekom, IBM, Intel, DELLEMC, and others in multi-million dollar
projects. He is a serial entrepreneur, the co-founder of Secret Double Octopus (doubleoctopus.com),
SecretSkyDB post-quantum data in rest, and SodsBC (SodsBC.com) post-quantum fastest
Blockchain.